We do cloud hosting, and then some...
Strato web hosting
Our Strato web hosting is ideal for those seeking a reliable, cost-effective hosting solution that is scalable and easy to use. It's the perfect solution for small to medium websites.
Optimized WordPress
Create a customizable and eye-catching site with ease. Optimized specifically for WordPress, our WordPress hosting includes enhanced performance, security, and specialist support.
Dedicated VPS hosting
Take control with dedicated resources in a virtual environment, offering greater customization, scalability, and autonomy compared to shared hosting.



- Websites hosted
- 15,000+
- Virtual machines
- 5,000+
- Domains hosted
- 100,000+
- Uptime
- 99.00%
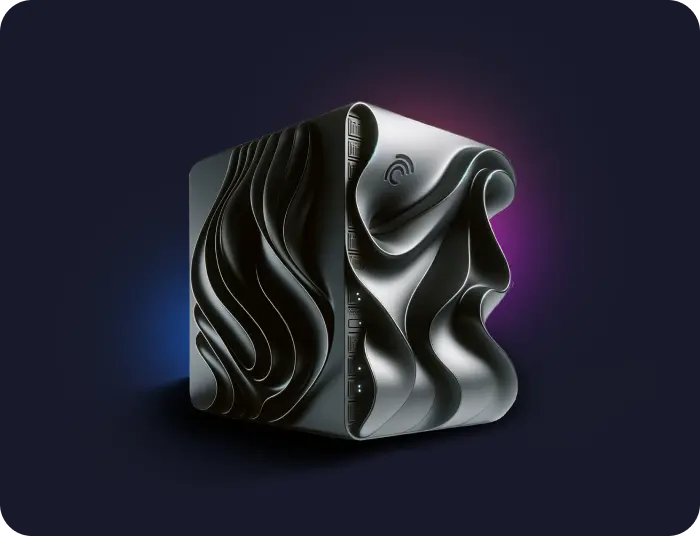
Why choose Cirrus Hosting?
Expert 24/7 support
Our friendly team of experts is available to answer any questions and solve any problem, from any time zone.
Flexible website solutions
With a range of plans, software systems, and add-ons, you′re sure to find just the right hosting solution for your needs and your budget.
Management made easy
We make site management simple, every step of the way - from setup and account management to billing and beyond.
Unbeatable server security
We protect our servers 24/7 with strict security protocols, including firewalls, on-site surveillance, biometric scanners, and more.
Trusted worldwide
We're a leading website, VPS, dedicated server, and cloud hosting provider – serving thousands of businesses in Canada, the US and worldwide.
Don't just take our word for it...
Your technical expertise has been top rate. I am extremely happy with Cirrus for meeting my service needs. The hosting provided has been seamless and ... show more
Kevin
We love to see a company that’s not only keeping its finger on the pulse of the industry but on the ebbs and flows of its customers’ needs. Cirrus Tec... show more
Alexandra Leslie
The HostingAdvice TeamWhen my VPS was breached by attackers, Cirrus worked with me to resolve and evolve my VPS to be even better. They’ve demonstrated a commitment to seei... show more
Mike
Little m DesignAward winning cloud hosting
Thanks to our customers, we have won many excellence awards for our web hosting and cloud services. We're grateful of the support, both from the industry and our customers, and hope to keep the quality of service the way our customers deserve.

May 2021
Top 10 Customer Service by HostAdvice

May 2012
Top 10 Cloud Hosting Provider by HostReview

May 2012
Top Pick Hosting company by Web Host Search

Aug 2007, Oct 2010
Top 10 Hosting company by HostReview

Jun 2009 - April 2011
Top 25 Most Popular Web Host by WebhostDir

Jun 2009 - April 2011
Most Popular Dedicated Hosting by Dedicated Server Directory

Feb 2009
Best Reseller Hosting by Dedicated Server Directory

Sept 2008
Best Windows Web Hosting by Webhostdir

Nov 2007 - Sept 2008
Top 10 Dedicated Servers by HostReview

Feb 2007
Best Budget Web Hosting plan by WebhostDir
Cirrus Hosting FAQs
Here are some of the most commonly asked questions about Cirrus Hosting. If you still can’t find the answer, just drop us a line on live chat and we'll be happy to help.
- Why Cirrus Hosting?
- Which plan is right for me?
- How long will it take for my account to be active?
- Do you charge any setup fees?
- What is web hosting?